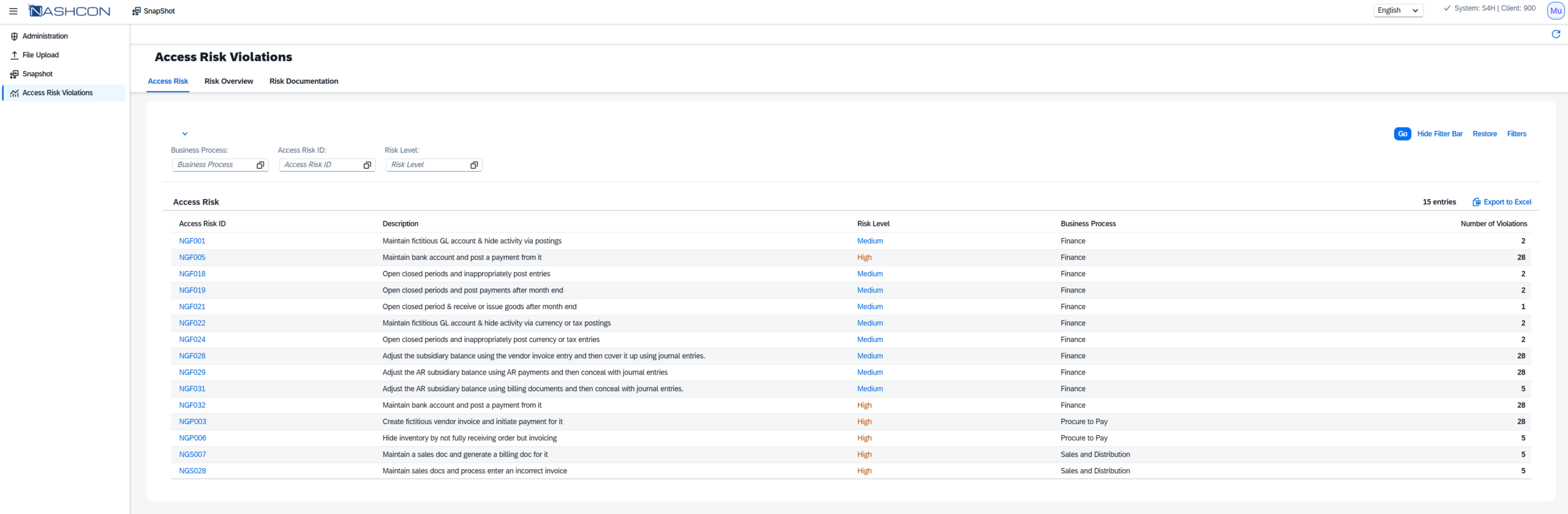
Access Risk Violations
Identify real SAP access risks — not just rule violations.
Access Risk Violations gives SAP Security, Audit and Compliance teams a clear view of critical authorization risks, SoD conflicts, affected users and documented mitigations — so open risks are visible, explainable and ready for remediation.
Built for: SAP Security • Internal Audit • GRC • Compliance • SAP Basis • Management
Open risk clarity
Separate unresolved access risks from mitigated and documented risks.
SoD conflict view
Understand segregation-of-duties conflicts by business process and risk level.
Auditor-ready evidence
Prepare structured findings with clear risk context and documentation.
SAP BTP deployment
Run the analysis in the SAP ecosystem and keep access-risk governance close to your SAP landscape.
Most SAP landscapes contain access risks. The hard part is knowing which ones still matter.
Traditional SAP risk reviews often stop at violation lists. But auditors and management need more: current risk exposure, mitigated vs. open risks, affected users, business process context and clear evidence for decisions.
Outdated rule sets
S/4HANA, Fiori and modern authorization risks are often not covered by legacy checks.
Open vs. mitigated is unclear
Without mitigation documentation, teams cannot distinguish accepted controls from unresolved exposure.
Too much manual analysis
Risk evidence is scattered across exports, spreadsheets and individual explanations.
From violation lists to risk decisions.
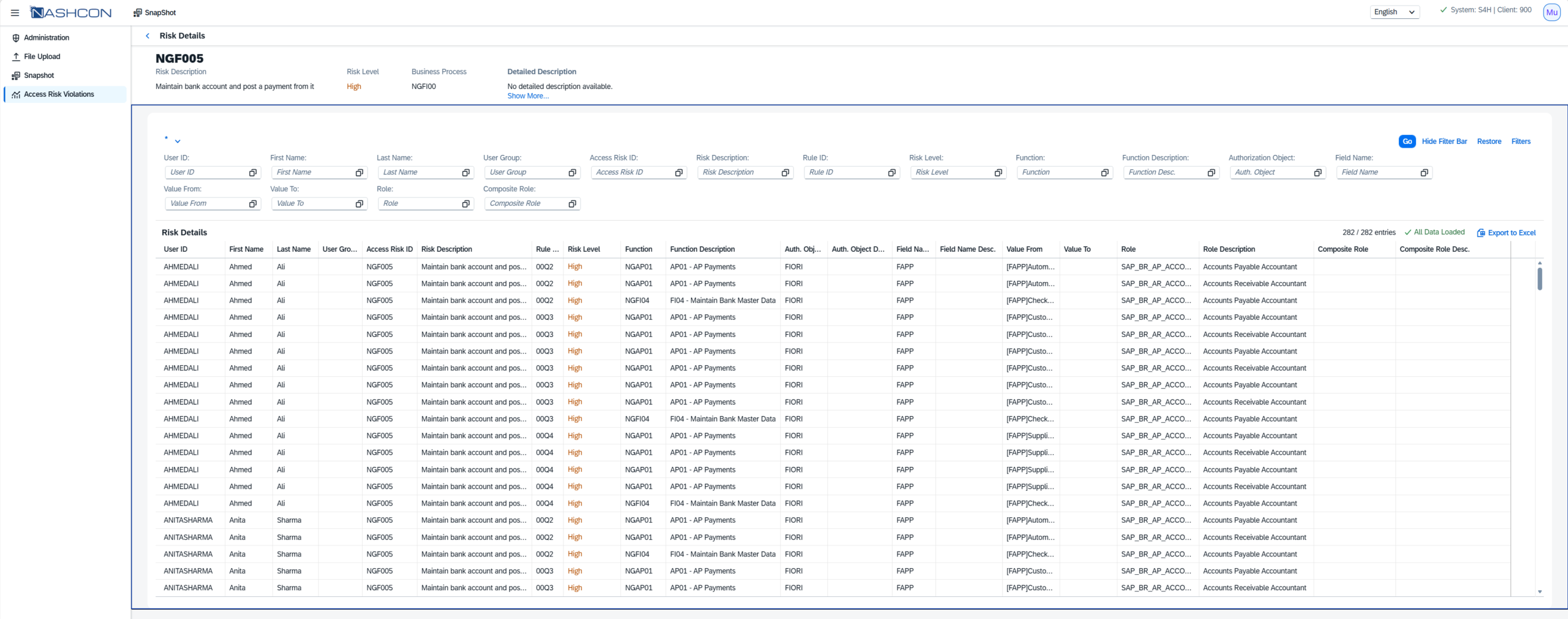
Access Risk Violations turns SAP authorization and SoD findings into a prioritized decision view: which risks exist, who is affected, how severe they are, whether mitigation exists and what needs to be documented or remediated.
Positioning: not a generic reporting page — a focused SAP GRC feature for access risk transparency and audit readiness.
Ready-to-use risk logic
Analyze critical actions, critical permissions and SoD conflicts without building a rule set from scratch.
Risk documentation
Document mitigations, ownership and review status so audit conversations are based on facts.
Business process context
Group violations by process, risk ID, level and affected users to find material exposure faster.
Management clarity
Translate technical findings into a clear picture of open risk, controlled risk and remediation focus.
A risk view auditors can actually use.
Give audit, SAP Security and compliance stakeholders a shared view of access risk violations — with filters, severity, business process context and documentation status.
Use it for: access risk reviews, SoD remediation, audit preparation, periodic controls, user risk analysis and management reporting.
A practical workflow from SAP data to remediation evidence.
No endless implementation project. The goal is fast visibility, structured documentation and a clear path from finding to action.
01
Collect
Capture relevant authorization, user and risk data from the evaluated SAP landscape.
02
Analyze
Evaluate violations against risk logic, SoD rules, business process and severity.
03
Separate
Distinguish open risks from mitigated, documented or accepted risk situations.
04
Act
Export evidence, assign ownership and drive remediation or management sign-off.
Built for the moments when SAP access risk becomes visible.
The feature supports the situations where teams need more than a list: audits, remediation planning, access reviews, management explanations and ongoing control monitoring.
Audit preparation
Prepare a clear evidence base for internal audit, external audit and compliance reviews.
SoD remediation
Prioritize conflicts by severity, affected users and business relevance before remediation starts.
Continuous access risk monitoring
Repeat the analysis regularly to detect new violations and track remediation progress.
Frequently asked questions.
Answers for SAP Security, GRC and Audit teams evaluating Access Risk Violations.
Access Risk Violations is designed for SAP authorization and GRC analysis scenarios. It can be used for SAP ERP and SAP S/4HANA landscapes where relevant authorization and risk data is available for evaluation.
It focuses on critical actions, critical permissions and segregation-of-duties conflicts. Findings can be viewed with risk context, severity, affected users and documentation status.
Risks with documented compensating controls or mitigation information can be treated separately from unresolved open risks. This helps auditors and management understand actual exposure instead of reviewing one mixed violation list.
Yes. The landing page positions the product around a structured, filterable risk view that supports internal audit, external audit preparation and compliance review discussions.
The goal is fast visibility after setup: collect the relevant SAP data, run the analysis, review open risks and use the findings for remediation, documentation or sign-off.
Yes. The product is positioned as part of the SAP BTP-based GRC Dashboard approach, keeping the analysis close to the SAP ecosystem instead of relying on disconnected external spreadsheets.
Yes. Existing compensating controls can be reflected in the documentation logic so teams can distinguish controlled risks from unresolved violations.
No. The feature is built for SAP Security, GRC, Compliance, Internal Audit, SAP Basis and Management stakeholders who need a shared understanding of access risk exposure.
Ready to see which SAP access risks are truly open?
Request a focused demo of Access Risk Violations and see how SAP authorization findings can become audit-ready risk decisions.