SAP System Security Configuration
Audit-ready SAP security parameters — governed on SAP BTP.
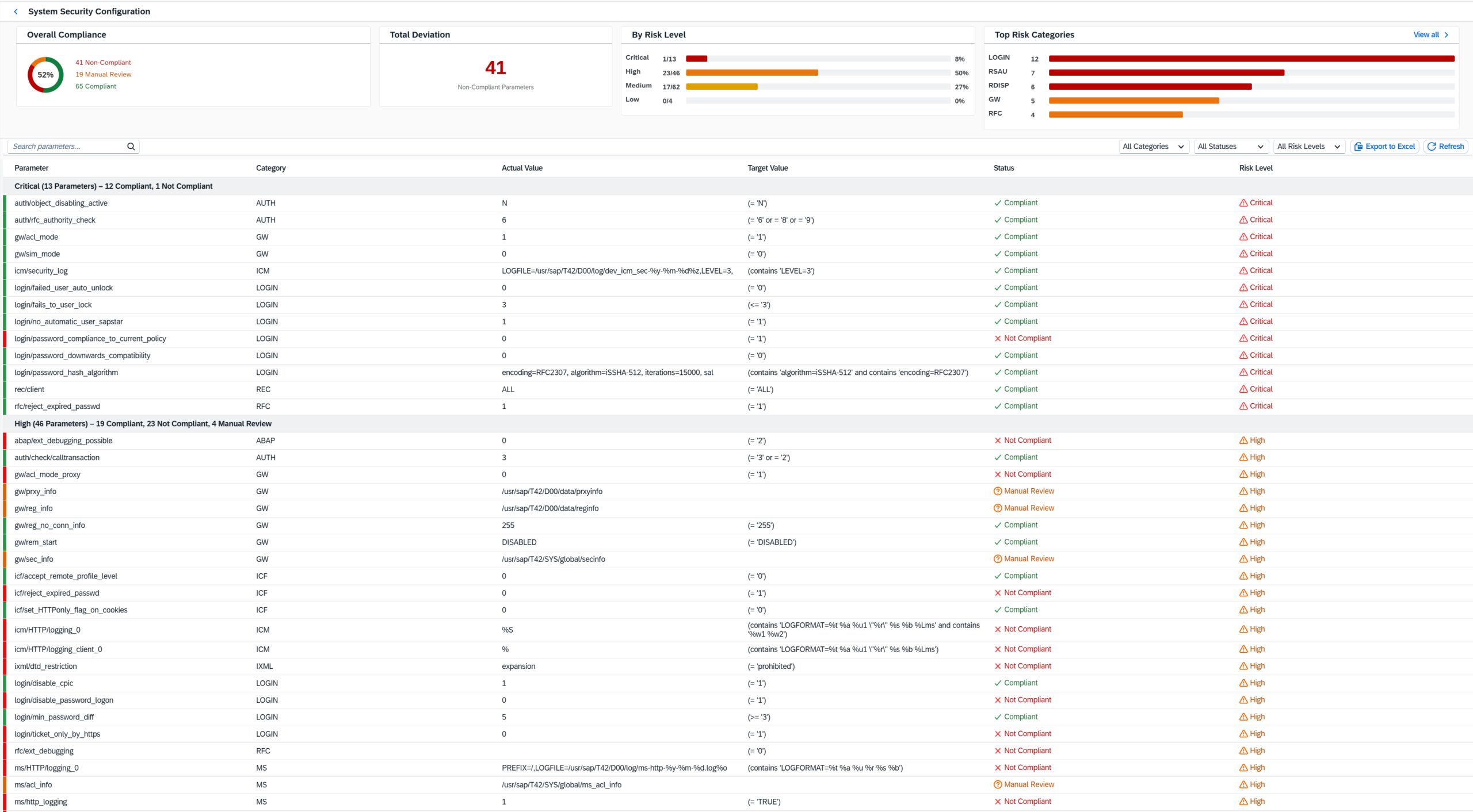
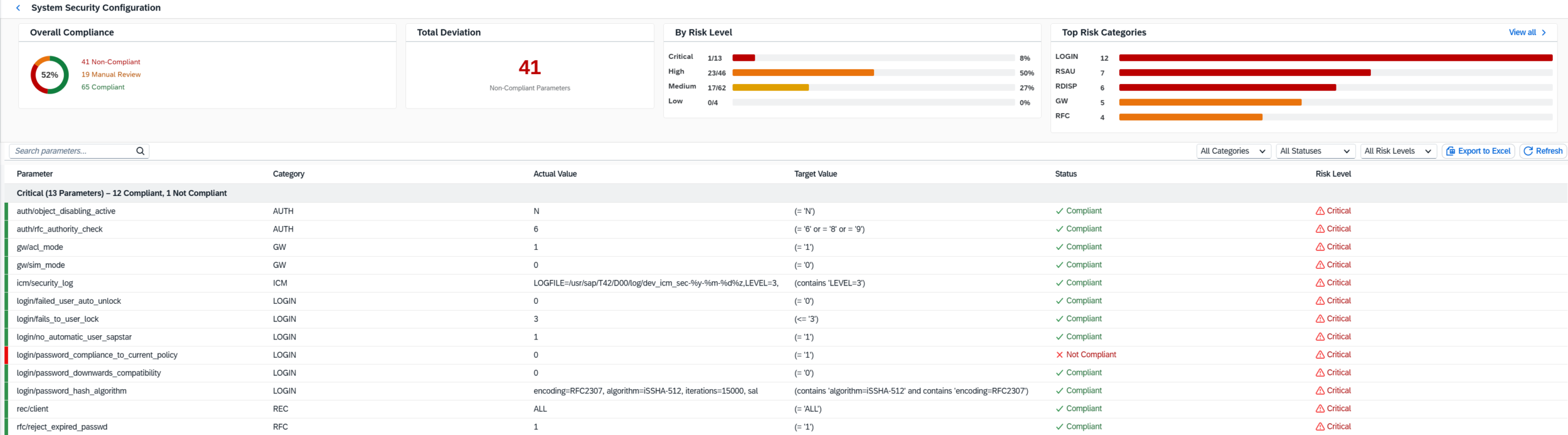
System Security Configuration turns SAP profile parameters and technical security settings into a clear compliance view: actual value, target value, status, risk level and remediation evidence — delivered as a focused SAP BTP application inside the SAP ecosystem.
For SAP Security, SAP Basis, Internal Audit and Compliance teams — designed for SAP BTP-based governance, transparency and audit readiness.
Overall compliance view
See overall posture immediately across compliant, non-compliant and manual-review parameters.
Risk-ranked findings
Critical and High deviations are separated from medium and low priority items.
SAP categories
Group issues by LOGIN, RFC, Gateway, ICM, RSAU, RDISP and other technical domains.
SAP BTP-native context
Present security configuration findings in a SAP ecosystem-aligned application, not in uncontrolled spreadsheet workflows.
Security-relevant SAP settings are too important to review manually.
Authentication behavior, password controls, RFC checks, gateway access, logging and system hardening depend on technical configuration values. When these values are reviewed through scattered exports, findings stay invisible too long and remediation becomes reactive.
The product answer: one focused System Security Configuration view that connects SAP parameter values, target rules, compliance status, risk severity and exportable evidence.
Parameter focus
SAP-specific profile parameters and technical security areas — not generic IT controls.
Target logic
Each finding shows actual value, expected target value and resulting compliance status.
Risk priority
Remediation starts where business and audit risk is highest.
Executive clarity
Compliance score and top categories turn technical data into a management-ready story.
Why SAP BTP matters for system security configuration.
SAP security and compliance reporting becomes stronger when it stays close to the SAP landscape. The SAP BTP-based approach supports a controlled, enterprise-ready operating model for analysis, review and audit communication.
The advantage: technical SAP parameter findings can be evaluated, explained and documented in a modern application layer without turning critical governance work into scattered files.
Operate inside the SAP ecosystem
Keep SAP security configuration analysis aligned with your SAP architecture and governance model.
Central compliance cockpit
Move from individual exports to a shared view for SAP Security, Basis, Audit and management.
Audit-ready evidence flow
Use consistent findings, status logic and exports as the basis for remediation tracking and sign-off.
Built for extension
Position System Security Configuration as a focused GRC dashboard capability that can evolve with further SAP security use cases.
One assessment view. Four decisions.
Designed to help teams understand what is compliant, what is not compliant, what needs manual review and where remediation should start.
Overall score, deviations and manual-review items in one executive summary.
Critical, High, Medium and Low classifications support remediation sequencing.
Top technical domains reveal where hardening gaps cluster.
Every row documents parameter, category, actual value, target value, status and risk level.
Three high-value use cases.
Baseline assessment
Create a clear baseline of SAP security parameter compliance across critical technical configuration areas.
Audit preparation
Prepare structured evidence for internal or external audit reviews without manual spreadsheet work.
Continuous hardening
Run recurring reviews, track progress and detect new non-compliant settings after changes.
From SAP parameter values to BTP-based audit evidence.
A simple workflow that connects SAP Basis, SAP Security, Audit and Management around the same facts.
01. Collect
Capture SAP security configuration data.
02. Evaluate
Compare actual values with target rules.
03. Prioritize
Rank by status, risk and category.
04. Evidence
Export findings for remediation and audit.
Frequently asked questions.
What exactly does System Security Configuration analyze?
Is this only a parameter list or does it provide a risk view?
Which statuses are used in the assessment?
Can we understand why a parameter matters?
How does SAP BTP add value here?
Does the solution change SAP system parameters automatically?
Can we filter and search the findings during an audit review?
What kind of management view does the product provide?
Can the results be exported for documentation?
Who is the feature built for?
See System Security Configuration on SAP BTP.
Review how SAP parameter checks, target-value logic, risk levels and BTP-based evidence can support your SAP security hardening and audit readiness.